[ad_1]

Getty Photos
Researchers have unearthed never-before-seen malware that hackers from North Korea have been utilizing to surreptitiously learn and obtain e-mail and attachments from contaminated customers’ Gmail and AOL accounts.
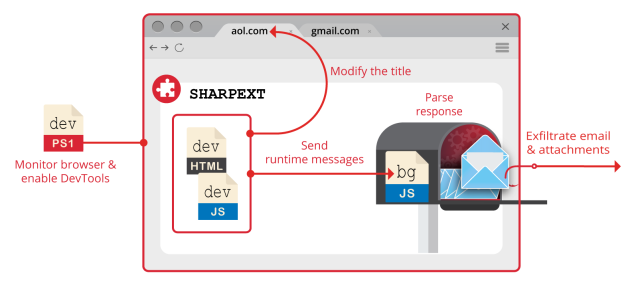
The malware, dubbed SHARPEXT by researchers from safety agency Volexity, makes use of intelligent means to put in a browser extension for the Chrome and Edge browsers, Volexity reported in a blog post. The extension cannot be detected by the e-mail companies, and for the reason that browser has already been authenticated utilizing any multifactor authentication protections in place, this more and more common safety measure performs no position in reining within the account compromise. The extension is not accessible in Google’s Chrome Internet Retailer, Microsoft’s add-ons web page, or some other recognized third-party supply and would not depend on flaws in Gmail or AOL Mail to get put in.
The malware has been in use for “nicely over a yr,” Volexity mentioned, and is the work of a hacking group the corporate tracks as SharpTongue. The group is sponsored by North Korea’s authorities and overlaps with a group tracked as Kimsuky by different researchers. SHARPEXT is focusing on organizations within the US, Europe, and South Korea that work on nuclear weapons and different points North Korea deems necessary to its nationwide safety.
Volexity President Steven Adair mentioned in an e-mail that the extension will get put in “by means of spear phishing and social engineering the place the sufferer is fooled into opening a malicious doc. Beforehand now we have seen DPRK menace actors launch spear phishing assaults the place your complete goal was to get the sufferer to put in a browser extension vs it being a publish exploitation mechanism for persistence and information theft.” In its present incarnation, the malware works solely on Home windows, however Adair mentioned there isn’t any cause it could not be broadened to contaminate browsers operating on macOS or Linux, too.
The weblog publish added: “Volexity’s personal visibility exhibits the extension has been fairly profitable, as logs obtained by Volexity present the attacker was in a position to efficiently steal hundreds of emails from a number of victims by way of the malware’s deployment.”
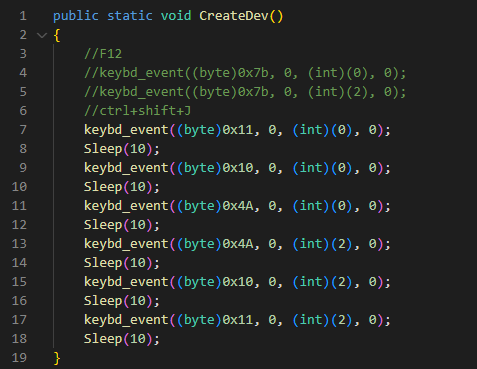
Putting in a browser extension throughout a phishing operation with out the end-user noticing is not straightforward. SHARPEXT builders have clearly paid consideration to analysis like what’s revealed here, here, and here, which exhibits how a safety mechanism within the Chromium browser engine prevents malware from making modifications to delicate consumer settings. Every time a respectable change is made, the browser takes a cryptographic hash of a few of the code. At startup, the browser verifies the hashes, and if any of them do not match, the browser requests the previous settings be restored.
For attackers to work round this safety, they need to first extract the next from the pc they’re compromising:
- A replica of the assets.pak file from the browser (which incorporates the HMAC seed utilized by Chrome)
- The consumer’s S-ID value
- The unique Preferences and Safe Preferences recordsdata from the consumer’s system
After modifying the desire recordsdata, SHARPEXT mechanically masses the extension and executes a PowerShell script that permits DevTools, a setting that permits the browser to run personalized code and settings.
“The script runs in an infinite loop checking for processes related to the focused browsers,” Volexity defined. “If any focused browsers are discovered operating, the script checks the title of the tab for a particular key phrase (for instance, ‘05101190,’ or ‘Tab+’ relying on the SHARPEXT model). The particular key phrase is inserted into the title by the malicious extension when an lively tab modifications or when a web page is loaded.”
Volexity
The publish continued:
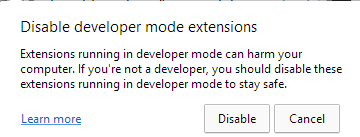
The keystrokes despatched are equal to
Management+Shift+J, the shortcut to allow the DevTools panel. Lastly, the PowerShell script hides the newly opened DevTools window through the use of the ShowWindow() API and theSW_HIDEflag. On the finish of this course of, DevTools is enabled on the lively tab, however the window is hidden.As well as, this script is used to cover any home windows that might alert the sufferer. Microsoft Edge, for instance, periodically shows a warning message to the consumer (Determine 5) if extensions are operating in developer mode. The script continually checks if this window seems and hides it through the use of the
ShowWindow()and theSW_HIDEflag.
Volexity
As soon as put in, the extension can carry out the next requests:
| HTTP POST Knowledge | Description |
| mode=record | Record beforehand collected e-mail from the sufferer to make sure duplicates should not uploaded. This record is constantly up to date as SHARPEXT executes. |
| mode=area | Record e-mail domains with which the sufferer has beforehand communicated. This record is constantly up to date as SHARPEXT executes. |
| mode=black | Accumulate a blacklist of e-mail senders that ought to be ignored when accumulating e-mail from the sufferer. |
| mode=newD&d=[data] | Add a site to the record of all domains considered by the sufferer. |
| mode=connect&title=[data]&idx=[data]&physique=[data] | Add a brand new attachment to the distant server. |
| mode=new&mid=[data]&mbody=[data] | Add Gmail information to the distant server. |
| mode=attlist | Commented by the attacker; obtain an attachments record to be exfiltrated. |
| mode=new_aol&mid=[data]&mbody=[data] | Add AOL information to the distant server. |
SHARPEXT permits the hackers to create lists of e-mail addresses to disregard and to maintain observe of e-mail or attachments which have already been stolen.
Volexity created the next abstract of the orchestration of the assorted SHARPEXT elements it analyzed:
Volexity
After this publish went stay, a Google spokesman emailed to reiterate that the extension wasn’t hosted on Google servers and that it was put in as post-exploit malware following a profitable phishing or social engineering assault.
anti-malware companies and utilizing safety hardened working methods like ChromeOS are greatest practices to forestall this and related forms of assaults
The weblog publish supplies photographs, file names, and different indicators that skilled individuals can use to find out if they’ve been focused or contaminated by this malware. The corporate warned that the menace it poses has grown over time and is not prone to go away any time quickly.
“When Volexity first encountered SHARPEXT, it gave the impression to be a instrument in early improvement containing quite a few bugs, a sign the instrument was immature,” the corporate mentioned. “The most recent updates and ongoing upkeep exhibit the attacker is reaching its targets, discovering worth in persevering with to refine it.”
Source link


