[ad_1]

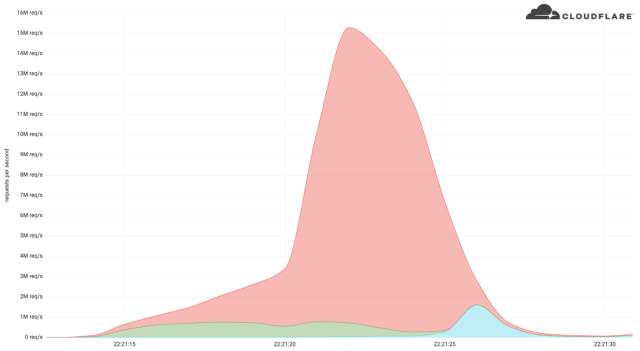
A cryptocurrency platform was not too long ago on the receiving finish of one of many greatest distributed denial-of-service assaults ever after menace actors bombarded it with 15.three million requests, content material supply community Cloudflare stated.
DDoS assaults could be measured in a number of methods, together with by the amount of information, the variety of packets, or the variety of requests despatched every second. The present information are 3.4 terabits per second for volumetric DDoSes—which try to eat all bandwidth accessible to the goal—809 million packets per second, and 17.2 million requests per second. The latter two information measure the ability of application-layer assaults, which try to exhaust the computing sources of a goal’s infrastructure.
Cloudflare’s latest DDoS mitigation peaked at 15.three million requests per second. Whereas nonetheless smaller than the report, its energy was extra appreciable as a result of the assault was delivered by HTTPS requests quite than HTTP requests used within the report. As a result of HTTPS requests are rather more compute-intensive than HTTP requests, the newest assault had the potential to place rather more pressure on the goal.
Cloudflare
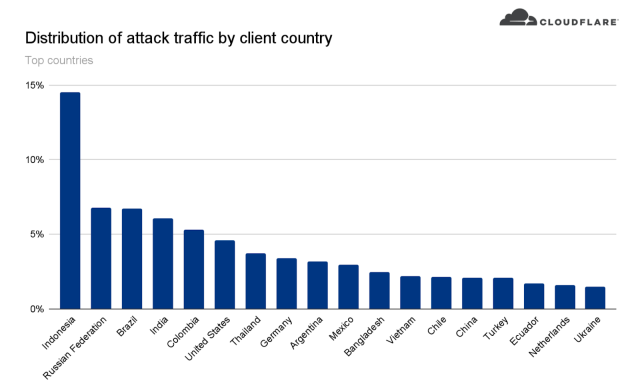
The sources required to ship the HTTPS request flood have been additionally better, indicating that DDoSers are rising more and more extra highly effective. Cloudflare stated that the botnet accountable, comprising about 6,000 bots, has delivered payloads as excessive as 10 million requests per second. The assault originated from 112 nations, with about 15 % of the firepower from Indonesia, adopted by Russia, Brazil, India, Colombia, and the US.
“Inside these nations, the assault originated from over 1,300 completely different networks,” Cloudflare researchers Omer Yoachimik and Julien Desgats wrote. They stated that the flood of visitors primarily got here from knowledge facilities, as DDoSes transfer away from residential community ISPs to cloud computing ISPs. High knowledge middle networks included the German supplier Hetzner On-line GmbH (Autonomous System Quantity 24940), Azteca Comunicaciones Colombia (ASN 262186), and OVH in France (ASN 16276). Different sources included residence and small workplace routers.
“On this case, the attacker was utilizing compromised servers on cloud internet hosting suppliers, a few of which look like operating Java-based purposes. That is notable due to the latest discovery of a vulnerability (CVE-2022-21449) that can be utilized for authentication bypass in a variety of Java-based purposes,” Cloudflare VP of Product Patrick Donahue wrote in an electronic mail. “We additionally noticed a major variety of MikroTik routers used within the assault, probably exploiting the identical vulnerability that the Meris botnet did.”
Cloudflare
The assault lasted about 15 seconds. Cloudflare mitigated it utilizing methods in its community of information facilities that mechanically detect visitors spikes and rapidly filter out the sources. Cloudflare didn’t establish the goal besides that it operated a crypto launchpad, a platform used to assist fund decentralized finance tasks.
The numbers underscore the arms race between attackers and defenders as every makes an attempt to outdo the opposite. It received’t be shocking if a brand new report is ready within the coming months.
Source link


